Computers & Technology
epub |eng | 2012-06-11 | Author:AnHai Doan & Alon Halevy & Zachary Ives
While manually constructed wrappers can be very powerful, they often incur labor cost that is impractical when dealing with a large number of data sources. Learning approaches, in contrast, consider ...
( Category:
Computer Science
November 21,2017 )
epub |eng | | Author:Xinpeng Xing, Peng Zhu & Georges Gielen
(4.3) If the clock of the VCO-based quantizer is not clean enough, it introduces an error in the quantization through two mechanisms: the sampling uncertainty triggered by pulse delay jitter ...
( Category:
Computers & Technology
November 21,2017 )
epub |eng | | Author:Chong-Min Kyung, Hiroto Yasuura, Yongpan Liu & Youn-Long Lin
10.4.1 Digital Filtering Digital filters are central to all signal processing systems. Each sample of the digitized signal is passed through a specific type of filter. Digital filters are used ...
( Category:
Engineering
November 21,2017 )
epub |eng | | Author:Peter Michler
(GHz) (GHz) (GHz) (ns) (ps) X 0.85 0 692 X 0.91 0 673 X 0.96 431 Using the above noise correlations, the time-integrated normalized two-photon correlation can be calculated, which ...
( Category:
Physics
November 21,2017 )
epub |eng | 2017-10-20 | Author:Perry Marshall
FIGURE 19.13–Mix It Up In this case, long copy works because the next step is a fairly big ask for cold traffic, so we felt that we needed a little ...
( Category:
Internet & Social Media
November 21,2017 )
epub, mobi |eng | 2011-09-09 | Author:2011 [2011]
98 Chapter 3 Case stUdIes: the sYstem Figure 3 .5 selecting syskey Decoder In Cain tools menu Figure 3 . 6 boot key selected When the Syskey Decoder dialog appears, ...
( Category:
Programming
November 20,2017 )
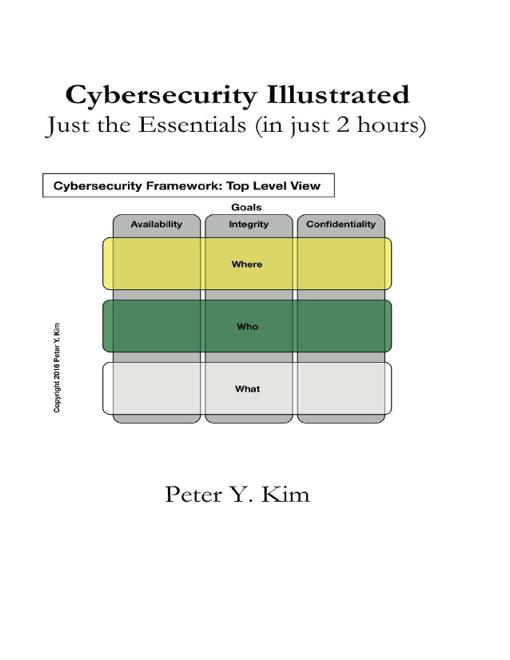
epub |eng | 2016-12-11 | Author:Kim, Peter
If your organization is doing a good job practicing the above security measures, you may deem those security measures sufficient. Implementing the above security measures may be easy for a ...
( Category:
Computers & Technology
November 20,2017 )
mobi |eng | 2016-12-10 | Author:Peter Kim
If your organization is doing a good job practicing the above security measures, you may deem those security measures sufficient. Implementing the above security measures may be easy for a ...
( Category:
Computers & Technology
November 20,2017 )
azw3, pdf |eng | 2016-12-11 | Author:Peter Kim [Kim, Peter]
If your organization is doing a good job practicing the above security measures, you may deem those security measures sufficient. Implementing the above security measures may be easy for a ...
( Category:
Computers & Technology
November 20,2017 )
mobi, epub |eng | | Author:2016
Conducting a hypothesis test There are multiple types of hypothesis tests out there, and among them are dozens of different procedures and metrics. Nonetheless, there are five basic steps that ...
( Category:
Computer Science
November 20,2017 )
epub |eng | | Author:2013
Note Note that Unobtrusive AJAX is the latest evolution of AJAX. This version of AJAX presents a clean separation of behavior (JavaScript), content (HTML), and presentation (CSS), and can work ...
( Category:
Programming
November 20,2017 )
epub |eng | 2013-07-23 | Author:Stibel, Jeff [Stibel, Jeff]
Nine Pheromones | Language | Mirrors Despite their minimal brainpower and inability to speak, ants are remarkably good at communicating, which they do automatically through scent. Their bodies are covered ...
( Category:
Skills
November 20,2017 )
epub |eng | 2017-11-02 | Author:Laine Campbell
Number of rows impacted is greater than N Alters on tables with a certain dataset size Alters on tables stored in metadata as too busy to have live alters on ...
( Category:
Computers & Technology
November 20,2017 )
epub |eng | | Author:Friedrich Recknagel & William K. Michener
11.3.2 Modeling the Relationship Among Watershed Physiography, Land Use Patterns, and Phosphorus Loading One of the emerging imperatives of eutrophication management is the advancement of our understanding of the relationships ...
( Category:
Computers & Technology
November 20,2017 )
azw3, epub |eng | 2017-08-24 | Author:Novick, Vladimir [Novick, Vladimir]
( Category:
Web Development & Design
November 20,2017 )
Categories
Popular ebooks
Deep Learning with Python by François Chollet(28998)The Mikado Method by Ola Ellnestam Daniel Brolund(26290)
Hello! Python by Anthony Briggs(25216)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(24446)
Kotlin in Action by Dmitry Jemerov(23535)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(22880)
Dependency Injection in .NET by Mark Seemann(22667)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(21430)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(20273)
Grails in Action by Glen Smith Peter Ledbrook(19343)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17056)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(16366)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(14077)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(12255)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11533)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10643)
Hit Refresh by Satya Nadella(9219)
The Kubernetes Operator Framework Book by Michael Dame(8579)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8432)
Robo-Advisor with Python by Aki Ranin(8376)